[ Car Hacking — Guides & Tutorials ]
Long-form material for the car-hacking section. Two flavours:
Tutorials hands-on walkthroughs where you DO something
(set up a virtual CAN lab, sniff UDS traffic from a
known-good scan tool, etc.). Run-along format.
Reference Guides read-once material that explains a protocol,
a module, or an architectural pattern. Look-up format.
For the scripts these guides are built around, the hardware reference,
and the curated link list, see the Car Hacking parent page.
[ Tutorials ]
Python Canbus Lab Guide — 05.2026
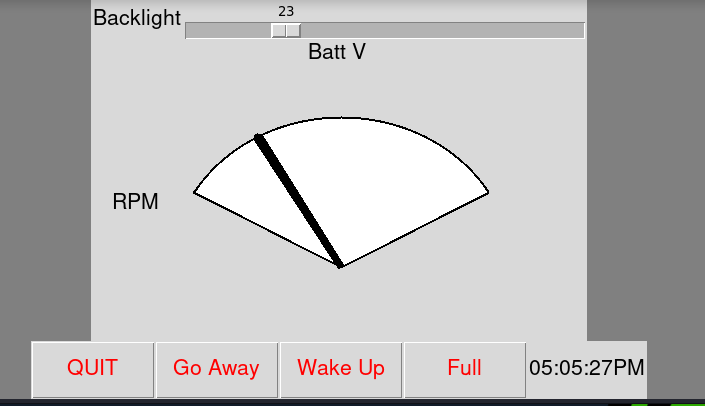
Hands-on lab for learning CAN bus reverse-engineering WITHOUT a real vehicle. Install py-can + can-utils, bring up a pair of virtual CAN interfaces (vcan0 / vcan1 to mirror CAN-IHS / CAN-C), replay a captured drive log via canplayer, and watch the traffic in tkcan.py or the newer pyJeepCan.py curses dashboard. Includes candump format walkthrough, a worked $12B decode example, a verifiable "what you should observe" checklist, cross-links to the Bus & Message Reference for ID lookups, and teardown commands. Download: tkcan.py (Tk viewer) | pyJeepCan.py (curses viewer) | CANBus Log Files
Reverse Engineering UDS with JScan — 05.2026
Hands-on intro to UDS reverse-engineering, using JScan as a known-good stimulus tool. Connect JScan, click a Live-Data field or an Activation, sniff what JScan sends withisotpdumpandcandump, decode the protocol byte-by-byte. The walkthrough covers Service 0x22 (ReadDataByIdentifier — reading battery voltage via DID $D020 on the HVAC module's $783/$503 ID pair) and Service 0x2F (IOControlByIdentifier — honking the horn via DID $D0AD on the BCM's $620/$504 pair). Also walks through the "request_service + 0x40 = positive response" rule and the 0x7F negative-response form, both of which carry across every other UDS service. Includes pointers to the Bus & Message Reference, horn.sh, and 3rd_brakelight.sh as natural follow-ons. Original walkthrough by jmccorm; page polish by magikh0e. Same technique applies to any UDS-speaking diagnostic tool (wiTECH, Autel, Launch X431, Topdon) — JScan is just the example.
[ Reference Guides ]
FCA CAN Bus & Message Reference — 05.2026
CAN-C vs CAN-IHS topology, TIPM/TIPMCGW gateway behavior, and decoded message IDs with byte-level evidence lifted from the scripts above — $1C0 RKE payloads, $122 ignition state, $350 RTC layout, the UDS service path used by 3rd_brakelight.sh ($2D3 / $620 / DID $D1B3), and the full JEEP live-data message map extracted from pyJeepCan.py. Includes candidate IDs for unverified next-additions (fuel level, throttle, TPMS, ambient temp, etc.) and caveats on model/year variance.
UDS Write Operations on FCA / Stellantis — 05.2026
The shared pattern behind every actuator-control script on the parent page (3rd_brakelight, horn / 3honk, 2k). Covers UDS Services 0x2F (IOControl), 0x2E (WriteDataByIdentifier), 0x31 (RoutineControl), and 0x27 (SecurityAccess); the two cleanup patterns (toggle-and-release vs hold-via-TesterPresent); known writable targets with verified DIDs and routine IDs; SGW interaction (what passes through the OBD-II port vs what requires direct CAN access); and the safety discipline that separates a useful demo from a bricked module.
Secure Gateway Module (SGW / SGM) — 05.2026
Reference guide to the FCA / Stellantis Secure Gateway Module on 2018+ vehicles — what it is, why it sits between the OBD-II port and the rest of the CAN bus, what it gates (writes blocked, reads allowed), how AutoAuth authentication works, hardware bypass options and their trade-offs, and how the SGW relates to the Uconnect head unit. Written from the perspective of someone working on these cars rather than someone selling a $5,000 scan tool.
In-Vehicle Event Handlers — 05.2026
The shared architectural pattern behind every state-change automation script on the parent page (Blackbox_monitor, autocollect, Remote_WiFi, backlight). Covers the candump + state-machine loop structure, edge vs level triggering, three rate-limiting strategies, three cleanup disciplines (explicit reset, deliberate non-reset, restore-to-safe), hardware lifecycle integration (crank brown-out, vehicle sleep, SD card flush), bus-quiet reconnect handling, and a worked example for adding your own handler for a new message ID.
Bridge between raw candump sniffing and UDS diagnostics work. Covers the CAN vs ISO-TP mental model, ISO-TP frame types (SF / FF / CF / FC) with byte layouts, isotpdump invocation and argument walkthrough, how to discover tester/ECU ID pairs on a target platform, and a worked Single Frame example matching the 3rd_brakelight.sh UDS request.